You might think that file encryption is just a minor detail in the grand scheme of data management, but it’s actually the linchpin of your organization’s cybersecurity strategy. With the rise in data breaches, understanding the implications of the Complete File – 8179999302 is crucial. It raises essential questions about your data handling practices and the potential risks lurking within sensitive files. What best practices should you adopt to ensure your information remains secure?
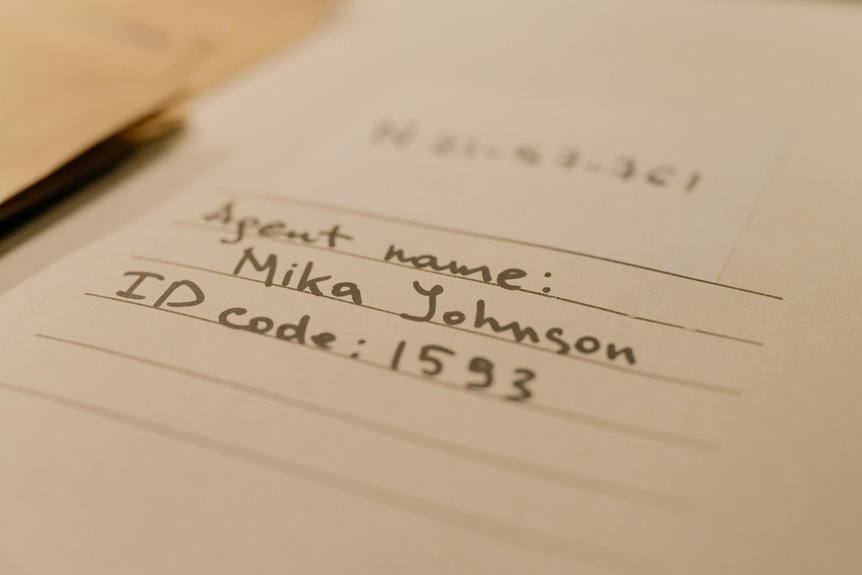
Understanding the Content of Complete File – 8179999302
Understanding the content of Complete File – 8179999302 requires a close examination of its components and structure.
You’ll find that file encryption plays a crucial role in securing sensitive information. Additionally, data classification helps in organizing this information effectively, enabling easier access and management.
Implications for Cybersecurity and Data Management
The interplay between file encryption and data classification significantly shapes the landscape of cybersecurity and data management.
By prioritizing encryption, you can mitigate the risk of data breaches, ensuring compliance with privacy regulations.
This strategic approach not only safeguards sensitive information but also enhances your organization’s resilience against evolving cyber threats, allowing you to maintain trust and uphold your commitment to data security.
Identifying Potential Risks Associated With Sensitive Files
While organizations strive to protect sensitive files, a variety of potential risks can undermine their efforts. Conducting a thorough risk assessment is crucial in identifying vulnerabilities.
Without proper file classification, sensitive information may be mishandled or exposed, leading to data breaches.
Best Practices for Handling Sensitive Information
To effectively handle sensitive information, organizations must adopt a set of best practices that prioritize security and compliance.
Implement data encryption to protect information during transmission and storage, ensuring unauthorized access is minimized.
Stay updated on privacy regulations to maintain compliance and avoid penalties.
Regularly train employees on these protocols, fostering a culture of awareness and responsibility regarding sensitive data management.
Conclusion
In conclusion, prioritizing proactive practices in file encryption and data classification is pivotal for preserving privacy and protecting sensitive data. By staying vigilant and adhering to best practices, you can effectively mitigate risks and safeguard your organization against cybersecurity threats. Remember, a commitment to compliance and continuous training fosters a culture of security, ensuring that you remain one step ahead in the ever-evolving landscape of data management. Stay sharp, stay secure, and safeguard your sensitive information.