Like a well-oiled machine, the Complete File – 8281670105 transforms the way you manage and access your data. It streamlines your processes, minimizes errors, and enhances organization. But how can you fully harness its potential while ensuring your sensitive information remains secure? Understanding its importance and best practices is crucial for empowering your decision-making. The key lies in implementing effective strategies that safeguard your digital assets.
Understanding the Importance of Complete File – 8281670105
Understanding the importance of Complete File – 8281670105 is crucial, especially if you’re navigating complex data management systems.
Recognizing the complete file benefits can enhance your efficiency, streamline processes, and reduce errors.
To maximize its potential, implement effective file organization tips, such as categorizing documents and using consistent naming conventions.
This structured approach fosters clarity and ultimately grants you greater freedom in managing your data.
Effective Utilization of Complete File – 8281670105
Maximizing the effectiveness of Complete File – 8281670105 hinges on strategic usage.
Focus on robust file organization to enhance data retrieval. By structuring your files intuitively, you streamline access, allowing you to locate information swiftly.
Embrace digital tools that promote efficiency, ensuring you maintain control over your data. This approach not only saves time but also empowers your decision-making process.
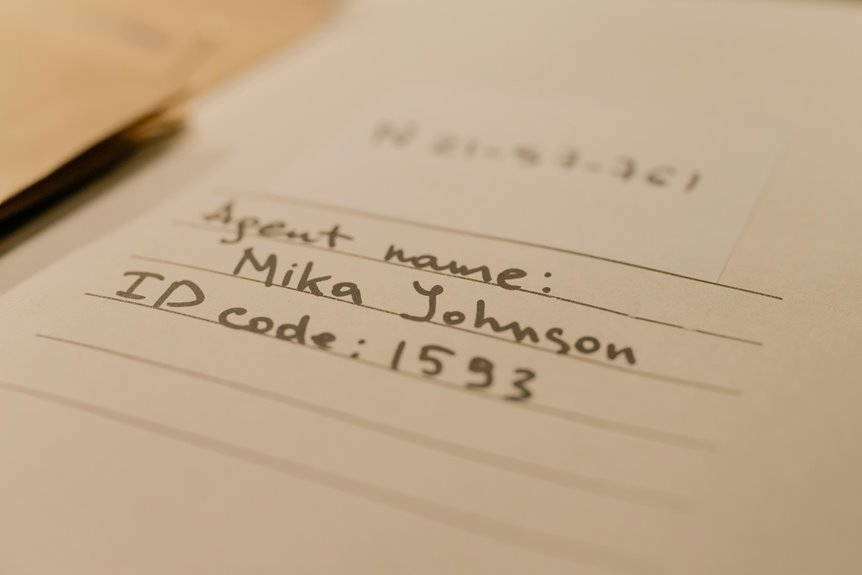
Best Practices for Managing Sensitive Information
When handling sensitive information, it’s crucial to implement best practices that safeguard your data from unauthorized access.
Utilize data encryption to protect stored information, and enforce access control measures to limit who can view it.
Invest in user training to ensure everyone understands their responsibilities.
Additionally, establish a robust incident response plan to quickly address any security breaches that may occur.
Strategies for Safeguarding Your Digital Assets
As digital threats continue to evolve, safeguarding your digital assets becomes increasingly vital.
Employ data encryption to protect sensitive information, ensuring unauthorized users can’t access your data.
Additionally, invest in robust cloud security solutions that offer encryption and threat detection.
Regularly update your software and back up your files to mitigate risks.
These strategies empower you to maintain control over your digital landscape.
Conclusion
In a world where data drives decisions, mastering the Complete File – 8281670105 can be your secret weapon. By implementing its structured approach, you not only boost efficiency but also enhance your ability to safeguard sensitive information. Think of it as your digital fortress; without strong walls, what’s to stop intruders? Embrace these practices to empower your data management, ensuring you stay ahead in an ever-evolving landscape while making informed choices with confidence.